Terminology
VRF – A VRF instance is a per-VPN routing information repository that defines the VPN membership of a customer site attached to the Provider Edge (PE) router. A VRF comprises an IP routing table, a derived Cisco Express Forwarding (CEF) table, a set of interfaces that use the forwarding table, and a set of rules and routing protocol parameters that control the information that is included in the routing table. A separate set of routing and Cisco Express Forwarding (CEF) tables is maintained for each VPN customer.
Inside VRF (IVRF) – Inside VRF contains the clear-text traffic (before encryption for outbound flows and after decryption for inbound flows). Typically, Each customer link has its own VRF instance configured on PE Routers, exchanged routing via MP-BGP and route traffic over MPLS network.
Front Door VRF (FVRF) – Front-door VRF (or outside VRF), the VRF that contain the encrypted traffic. Typically, this VRF is used for internet traffic and VPN endpoint IP addresses are part of this VRF.
Global VRF – The routing instance that is used if no specific VRF is defined. If there is no VRF instance configured on interface, that interface belongs to global VRF.
VRF-Aware IPsec Functional Overview
Front Door VRF (FVRF) and Inside VRF (IVRF) are central to understanding the feature.
Each IPsec tunnel is associated with two VRF domains. The outer encapsulated packet belongs to one VRF domain, which we shall call the FVRF, while the inner, protected IP packet belongs to another domain called the IVRF. Another way of stating the same thing is that the local endpoint of the IPsec tunnel belongs to the FVRF while the source and destination addresses of the inside packet belong to the IVRF.
One or more IPsec tunnels can terminate on a single interface. The FVRF of all these tunnels is the same and is set to the VRF that is configured on that interface. The IVRF of these tunnels can be different and depends on the VRF that is defined in the Internet Security Association and Key Management Protocol (ISAKMP) profile that is attached to a crypto map entry.
Packet Flow into the IPsec Tunnel
- A VPN packet arrives from the Service Provider MPLS backbone network to the PE and is routed through an interface facing the Internet.
- The packet is matched against the Security Policy Database (SPD), and the packet is IPsec encapsulated. The SPD includes the IVRF and the access control list (ACL).
- The IPsec encapsulated packet is then forwarded using the FVRF routing table.
Packet Flow from the IPsec Tunnel
- An IPSec-encapsulated packet arrives at the PE router from the remote IPsec endpoint.
- IPSec performs the Security Association (SA) lookup for the Security Parameter Index (SPI), destination, and protocol.
- The packet is decapsulated using the SA and is associated with IVRF.
- The packet is further forwarded using the IVRF routing table.
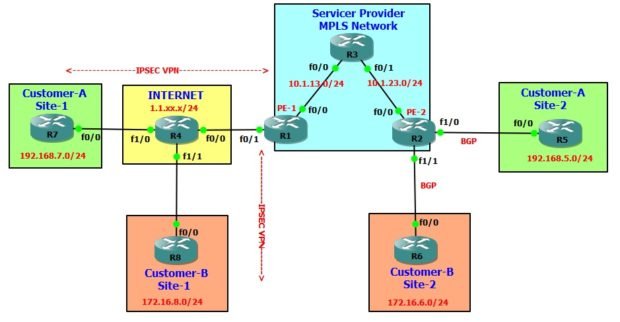
Network Topology
IP Addressing
| Hostname | Interface | IP Address |
| R1 | Fa0/0 | 10.1.13.1/24 |
| R1 | Fa0/1 | 1.1.14.1/24 |
| R1 | Loopback0 | 10.1.0.1/32 |
| R2 | Fa0/0 | 10.1.23.2/24 |
| R2 | Fa1/0 | 10.10.25.2/24 |
| R2 | Fa1/1 | 10.10.26.2/24 |
| R2 | Loopback0 | 10.1.0.2/32 |
| R3 | Fa0/0 | 10.1.13.3/24 |
| R3 | Fa0/1 | 10.1.23.3/24 |
| R3 | Loopback0 | 10.1.0.3/32 |
| R4 | Fa0/0 | 1.1.14.4/24 |
| R4 | Fa1/0 | 1.1.47.4/24 |
| R4 | Fa1/1 | 1.1.48.4/24 |
| R5 | Fa0/0 | 10.10.25.5/24 |
| R5 | Fa0/1 | 192.168.5.5/24 |
| R6 | Fa0/0 | 10.10.26.6/24 |
| R6 | Fa0/1 | 172.16.6.6/24 |
| R7 | Fa0/0 | 1.1.47.7/24 |
| R7 | Fa0/1 | 192.168.7.7/24 |
| R8 | Fa0/0 | 1.1.48.8/24 |
| R8 | Fa0/1 | 172.16.8.8/24 |
Note: We will not discuss MPLS, BGP Configuration, It is assumed that you have basic knowledge of MPLS, MP-BGP configuration. This discussion is limited to VRF Aware IPSEC VPN only.
Configuration:
R1 is PE Router which has one arm connected to internal MPLS network and other arm is connected to Internet. The same internet link will be shared for VRF Aware IPSec VPN of multiple customers.
Here, we will not configure any VRF instance for Internet link, hence it will be treated as Global VRF. We will create and discuss VRF instance for internet link in part-2 of this topic.
R1 - PE and VRF Aware IPSec VPN Router !! -- Create VRF named cust-a for Customer-A --!! !! -- This is Inside VRF (I-VRF) --!! vrf definition cust-a rd 123:1 ! address-family ipv4 route-target export 123:1 route-target import 123:1 exit-address-family ! !! -- Create VRF named cust-b for Customer-B --!! !! -- This is Inside VRF (I-VRF) --!! ! vrf definition cust-b rd 123:2 ! address-family ipv4 route-target export 123:2 route-target import 123:2 exit-address-family ! !! -- Define ISAKMP Pre-shared key for both VPNs --!! ! crypto keyring vpn1 pre-shared-key address 1.1.47.7 key vpn1password crypto keyring vpn2 pre-shared-key address 1.1.48.8 key vpn2password ! !! -- Create ISAKMP Policy --!! ! crypto isakmp policy 1 encr 3des authentication pre-share group 2 ! !! -- Create ISAKMP Profile for both VPNs --!! ! crypto isakmp profile vpn1 vrf cust-a keyring vpn1 match identity address 1.1.47.7 255.255.255.255 crypto isakmp profile vpn2 vrf cust-b keyring vpn2 match identity address 1.1.48.8 255.255.255.255 ! ! !! -- Create IPSec Transform-set for both VPNs --!! ! crypto ipsec transform-set vpn1-TS esp-3des esp-sha-hmac mode tunnel crypto ipsec transform-set vpn2-TS esp-3des esp-sha-hmac mode tunnel ! ! !! -- Create access-list to define the traffic to pass through --!! !! -- the VPN tunnel --!! !! -- access-list 101 is for Customer-1 traffic --!! !! -- access-list 102 is for Customer-2 traffic --!! ! access-list 101 permit ip 192.168.5.0 0.0.0.255 192.168.7.0 0.0.0.255 access-list 102 permit ip 172.16.6.0 0.0.0.255 172.16.8.0 0.0.0.255 ! !! -- Create Crypto MAP for both VPNs --!! ! crypto map crypmap 1 ipsec-isakmp set peer 1.1.47.7 set transform-set vpn1-TS set isakmp-profile vpn1 match address 101 ! crypto map crypmap 2 ipsec-isakmp set peer 1.1.48.8 set transform-set vpn2-TS set isakmp-profile vpn2 match address 102 ! !! -- Apply Crypto MAP to Internet facing interface --!! ! interface FastEthernet0/1 ip address 1.1.14.1 255.255.255.0 crypto map crypmap ! !! -- Routing --!! !! -- Configure a default static route via internet next-hop IP --!! !! -- There is no VRF defined for Internet link --!! !! -- By default it belongs to Global VRF --!! ! ip route 0.0.0.0 0.0.0.0 1.1.14.4 ! !! -- As VPN Peer IP is reachable via internet link of Global VRF --!! !! -- We have to define below routes to route traffic --!! !! -- from customer VRF to Global VRF--!! ! ip route vrf cust-a 192.168.7.0 255.255.255.0 1.1.14.4 global ip route vrf cust-b 172.16.8.0 255.255.255.0 1.1.14.4 global ! !! -- Redistribute IPSec VPN routes into BGP --!! !! -- MP-BGP will advertise it to PE-2 Router --!! !! -- PE-2 Router will advertise those routes to Customers --!! ! router bgp 123 bgp router-id 10.1.0.1 bgp log-neighbor-changes no bgp default ipv4-unicast neighbor 10.1.0.2 remote-as 123 neighbor 10.1.0.2 update-source Loopback0 ! address-family ipv4 exit-address-family ! address-family vpnv4 neighbor 10.1.0.2 activate neighbor 10.1.0.2 send-community extended exit-address-family ! address-family ipv4 vrf cust-a redistribute static exit-address-family ! address-family ipv4 vrf cust-b redistribute static exit-address-family !
Verification: R7 (Customer-A Site 1) can ping R5 (Customer-A Site-2) network R7#ping 192.168.5.5 so 192.168.7.7 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 192.168.5.5, timeout is 2 seconds: Packet sent with a source address of 192.168.7.7 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 172/184/196 ms R8 (Customer-B Site 1) can ping R6 (Customer-B Site-2) network R8#ping 172.16.6.6 so 172.16.8.8 Type escape sequence to abort. Sending 5, 100-byte ICMP Echos to 172.16.6.6, timeout is 2 seconds: Packet sent with a source address of 172.16.8.8 !!!!! Success rate is 100 percent (5/5), round-trip min/avg/max = 152/164/188 ms Verify VPN Status on R1 R1#show crypto session detail Crypto session current status Code: C - IKE Configuration mode, D - Dead Peer Detection K - Keepalives, N - NAT-traversal, T - cTCP encapsulation X - IKE Extended Authentication, F - IKE Fragmentation Interface: FastEthernet0/1 Profile: vpn1 Uptime: 00:40:13 Session status: UP-ACTIVE Peer: 1.1.47.7 port 500 fvrf: (none) ivrf: cust-a Phase1_id: 1.1.47.7 Desc: (none) IKEv1 SA: local 1.1.14.1/500 remote 1.1.47.7/500 Active Capabilities:(none) connid:1001 lifetime:23:19:46 IPSEC FLOW: permit ip 192.168.5.0/255.255.255.0 192.168.7.0/255.255.255.0 Active SAs: 2, origin: crypto map Inbound: #pkts dec'ed 24 drop 0 life (KB/Sec) 4175257/1186 Outbound: #pkts enc'ed 24 drop 0 life (KB/Sec) 4175257/1186 Interface: FastEthernet0/1 Profile: vpn2 Uptime: 00:38:49 Session status: UP-ACTIVE Peer: 1.1.48.8 port 500 fvrf: (none) ivrf: cust-b Phase1_id: 1.1.48.8 Desc: (none) IKEv1 SA: local 1.1.14.1/500 remote 1.1.48.8/500 Active Capabilities:(none) connid:1002 lifetime:23:21:09 IPSEC FLOW: permit ip 172.16.6.0/255.255.255.0 172.16.8.0/255.255.255.0 Active SAs: 2, origin: crypto map Inbound: #pkts dec'ed 14 drop 0 life (KB/Sec) 4190264/1270 Outbound: #pkts enc'ed 14 drop 0 life (KB/Sec) 4190264/1270
Here is the configuration of all devices, if you want to understand and test it in your lab. ----------------------------------------------- R1 - MPLS PE-1 and VRF Aware IPSec VPN Router ----------------------------------------------- hostname R1 ! vrf definition cust-a rd 123:1 ! address-family ipv4 route-target export 123:1 route-target import 123:1 exit-address-family ! vrf definition cust-b rd 123:2 ! address-family ipv4 route-target export 123:2 route-target import 123:2 exit-address-family ! crypto keyring vpn1 pre-shared-key address 1.1.47.7 key vpn1password crypto keyring vpn2 pre-shared-key address 1.1.48.8 key vpn2password ! crypto isakmp policy 1 encr 3des authentication pre-share group 2 crypto isakmp profile vpn1 vrf cust-a keyring vpn1 match identity address 1.1.47.7 255.255.255.255 crypto isakmp profile vpn2 vrf cust-b keyring vpn2 match identity address 1.1.48.8 255.255.255.255 ! ! crypto ipsec transform-set vpn1-TS esp-3des esp-sha-hmac mode tunnel crypto ipsec transform-set vpn2-TS esp-3des esp-sha-hmac mode tunnel ! ! ! crypto map crypmap 1 ipsec-isakmp set peer 1.1.47.7 set transform-set vpn1-TS set isakmp-profile vpn1 match address 101 crypto map crypmap 2 ipsec-isakmp set peer 1.1.48.8 set transform-set vpn2-TS set isakmp-profile vpn2 match address 102 ! interface Loopback0 ip address 10.1.0.1 255.255.255.255 ip ospf 1 area 0 ! interface FastEthernet0/0 ip address 10.1.13.1 255.255.255.0 ip ospf network point-to-point ip ospf 1 area 0 speed 100 duplex full mpls ip ! interface FastEthernet0/1 ip address 1.1.14.1 255.255.255.0 speed 100 duplex full crypto map crypmap ! router ospf 1 router-id 10.1.0.1 ! router bgp 123 bgp router-id 10.1.0.1 bgp log-neighbor-changes no bgp default ipv4-unicast neighbor 10.1.0.2 remote-as 123 neighbor 10.1.0.2 update-source Loopback0 ! address-family ipv4 exit-address-family ! address-family vpnv4 neighbor 10.1.0.2 activate neighbor 10.1.0.2 send-community extended exit-address-family ! address-family ipv4 vrf cust-a redistribute static exit-address-family ! address-family ipv4 vrf cust-b redistribute static exit-address-family ! ip route 0.0.0.0 0.0.0.0 1.1.14.4 ip route vrf cust-a 192.168.7.0 255.255.255.0 1.1.14.4 global ip route vrf cust-b 172.16.8.0 255.255.255.0 1.1.14.4 global ! access-list 101 permit ip 192.168.5.0 0.0.0.255 192.168.7.0 0.0.0.255 access-list 102 permit ip 172.16.6.0 0.0.0.255 172.16.8.0 0.0.0.255 ! end ---------------------- R2 - MPLS PE-2 Router ---------------------- hostname R2 ! vrf definition cust-a rd 123:1 ! address-family ipv4 route-target export 123:1 route-target import 123:1 exit-address-family ! vrf definition cust-b rd 123:2 ! address-family ipv4 route-target export 123:2 route-target import 123:2 exit-address-family ! interface Loopback0 ip address 10.1.0.2 255.255.255.255 ip ospf 1 area 0 ! interface FastEthernet0/0 ip address 10.1.23.2 255.255.255.0 ip ospf network point-to-point ip ospf 1 area 0 speed 100 duplex full mpls ip ! interface FastEthernet1/0 vrf forwarding cust-a ip address 10.10.25.2 255.255.255.0 speed 100 duplex full ! interface FastEthernet1/1 vrf forwarding cust-b ip address 10.10.26.2 255.255.255.0 speed 100 duplex full ! router ospf 1 router-id 10.1.0.2 ! router bgp 123 bgp router-id 10.1.0.2 bgp log-neighbor-changes no bgp default ipv4-unicast neighbor 10.1.0.1 remote-as 123 neighbor 10.1.0.1 update-source Loopback0 ! address-family ipv4 exit-address-family ! address-family vpnv4 neighbor 10.1.0.1 activate neighbor 10.1.0.1 send-community extended exit-address-family ! address-family ipv4 vrf cust-a redistribute connected redistribute static neighbor 10.10.25.5 remote-as 65005 neighbor 10.10.25.5 activate exit-address-family ! address-family ipv4 vrf cust-b redistribute connected redistribute static neighbor 10.10.26.6 remote-as 65006 neighbor 10.10.26.6 activate exit-address-family ! end ------------------- R3 - MPLS P Router ------------------- hostname R3 ! interface Loopback0 ip address 10.1.0.3 255.255.255.255 ip ospf 1 area 0 ! interface FastEthernet0/0 ip address 10.1.13.3 255.255.255.0 ip ospf network point-to-point ip ospf 1 area 0 speed 100 duplex full mpls ip ! interface FastEthernet0/1 ip address 10.1.23.3 255.255.255.0 ip ospf network point-to-point ip ospf 1 area 0 speed 100 duplex full mpls ip ! router ospf 1 router-id 10.1.0.3 ! end --------------------- R4 - Internet Router --------------------- hostname R4 ! interface FastEthernet0/0 ip address 1.1.14.4 255.255.255.0 speed 100 duplex full ! interface FastEthernet1/0 ip address 1.1.47.4 255.255.255.0 speed 100 duplex full ! interface FastEthernet1/1 ip address 1.1.48.4 255.255.255.0 speed 100 duplex full ! end --------------------------------- R5 - Customer A Site 2 CE Router --------------------------------- hostname R5 ! interface FastEthernet0/0 ip address 10.10.25.5 255.255.255.0 speed 100 duplex full ! interface FastEthernet0/1 ip address 192.168.5.5 255.255.255.0 speed auto duplex auto ! router bgp 65005 bgp log-neighbor-changes network 192.168.5.0 neighbor 10.10.25.2 remote-as 123 ! end --------------------------------- R6 - Customer-B Site 2 CE Router --------------------------------- hostname R6 ! interface FastEthernet0/0 ip address 10.10.26.6 255.255.255.0 speed 100 duplex full ! interface FastEthernet0/1 ip address 172.16.6.6 255.255.255.0 speed auto duplex auto ! router bgp 65006 bgp log-neighbor-changes network 172.16.6.0 mask 255.255.255.0 neighbor 10.10.26.2 remote-as 123 ! end -------------------------------------------------------------------- R7 - Customer-A Site 1 Router having Site-to-Site IPSec VPN with R1 -------------------------------------------------------------------- hostname R7 ! crypto isakmp policy 1 encr 3des authentication pre-share group 2 crypto isakmp key vpn1password address 1.1.14.1 ! crypto ipsec transform-set TS esp-3des esp-sha-hmac mode tunnel ! crypto map crypmap 1 ipsec-isakmp set peer 1.1.14.1 set transform-set TS match address 101 ! interface FastEthernet0/0 ip address 1.1.47.7 255.255.255.0 speed 100 duplex full crypto map crypmap ! interface FastEthernet0/1 ip address 192.168.7.7 255.255.255.0 speed auto duplex auto ! ip route 0.0.0.0 0.0.0.0 1.1.47.4 ! access-list 101 permit ip 192.168.7.0 0.0.0.255 192.168.5.0 0.0.0.255 ! end -------------------------------------------------------------------- R8 - Customer-B Site 1 Router having Site-to-Site IPSec VPN with R1 -------------------------------------------------------------------- hostname R8 ! crypto isakmp policy 1 encr 3des authentication pre-share group 2 crypto isakmp key vpn2password address 1.1.14.1 ! crypto ipsec transform-set TS esp-3des esp-sha-hmac mode tunnel ! crypto map crypmap 1 ipsec-isakmp set peer 1.1.14.1 set transform-set TS match address 102 ! interface FastEthernet0/0 ip address 1.1.48.8 255.255.255.0 speed 100 duplex full crypto map crypmap ! interface FastEthernet0/1 ip address 172.16.8.8 255.255.255.0 speed auto duplex auto ! ip route 0.0.0.0 0.0.0.0 1.1.48.4 ! access-list 102 permit ip 172.16.8.0 0.0.0.255 172.16.6.0 0.0.0.255 ! end